
TAYSIR ZEITUNI
Network & Security Engineer with 7+ years managing ISP infrastructure, firewalls, and enterprise networks. Penetration tester with real-world engagements in web application and network security — and a Front-End Developer who builds what he secures.
Why Choose Me
7+ years managing real ISP infrastructure, enterprise networks, and security systems — combined with hands-on penetration testing, SOC operations, and Front-End development. I don't just build for the web; I secure it from the ground up.
Taysir Zeituni
Network & Security Engineer · Pentester · Front-End Dev
Damascus, SyriaRoles
Core Stack
Education
Network & Infrastructure Management
7+ years managing full ISP infrastructure including core routers, switches, firewalls, and servers. Built a multi-tower wireless distribution network across three buildings using Mikrotik, Ubiquiti, and Mimosa. Deployed and maintained pfSense, OpenVPN, WireGuard, and Snort in production environments.
Penetration Testing & Bug Bounty
Conducted real-world web application penetration tests for a marketing company and a 2-year network security engagement for a banking institution. Actively hunting bugs on HackerOne, practicing on HackTheBox, TryHackMe, and Cyber Talents — with three CTF competition wins.
VoIP & Telecommunications
4+ years designing and managing IP communications systems using GrandStream, Yeastar, and SIP protocols. Configured PBX infrastructure, call routing, and unified communications solutions for enterprise environments.
Security Operations & Automation
Experienced with Security Onion, Wazuh, and Splunk for SOC monitoring and incident detection. Automates security workflows and recon pipelines using Python, Bash, and n8n — including an AI-powered bug bounty automation suite integrated with Google Gemini.
About Me
My journey, skills & experience
Who I Am
I am Taysir Zeituni, a Network & Security Engineer, Penetration Tester, and Front-End Developer. With 7+ years of hands-on experience managing ISP infrastructure, firewalls, and enterprise networks — alongside 4+ years in VoIP and telecommunications systems — I bring deep technical expertise across the full stack of networking and cybersecurity. I conduct penetration testing for web applications and banking networks, actively compete in CTF challenges, and build modern web interfaces using React and JavaScript. I am passionate about securing systems from the ground up — from core network architecture to application-layer vulnerabilities.
My Skills
Experience Journey
Network Manager – ISP
Internet Service Provider · SyriaManaged full network infrastructure including servers, routers, firewalls, and core ISP systems. Built and maintained a multi-tower wireless distribution network across three buildings using Mikrotik, Ubiquiti, and Mimosa equipment. Deployed and administered pfSense, OpenVPN, WireGuard, Snort, and Splunk for security and monitoring.
VoIP & Telecommunications Engineer
Network Communications · SyriaDesigned and managed IP communications systems using GrandStream, Yeastar, and SIP protocols. Configured and maintained PBX infrastructure, call routing, and unified communications solutions for enterprise environments.
Penetration Tester & Ethical Hacker
Self-Employed · SyriaConducted web application penetration testing for Phoenix Marketing & Sales. Performed network security assessments for a banking institution over a 2-year engagement. Actively practicing on HackTheBox, TryHackMe, and Cyber Talents platforms, with three CTF (Capture The Flag) competition achievements.
Front-End Developer
Self-Employed · SyriaDeveloped responsive web applications and websites using HTML, CSS, JavaScript, and React. Delivered full client projects with a focus on clean UI, performance, and applying secure coding practices throughout the development lifecycle.
Homelab Engineer & Security Researcher
Personal Lab · SyriaBuilt and maintain a personal training lab on a dedicated ESXi server running EVE-NG for hands-on network and security simulations. Experienced with Security Onion, Wazuh, Splunk, Docker, and Linux administration. Automates workflows using n8n, Python, and Bash scripting.
Projects
Real-world labs, security research, and automation builds
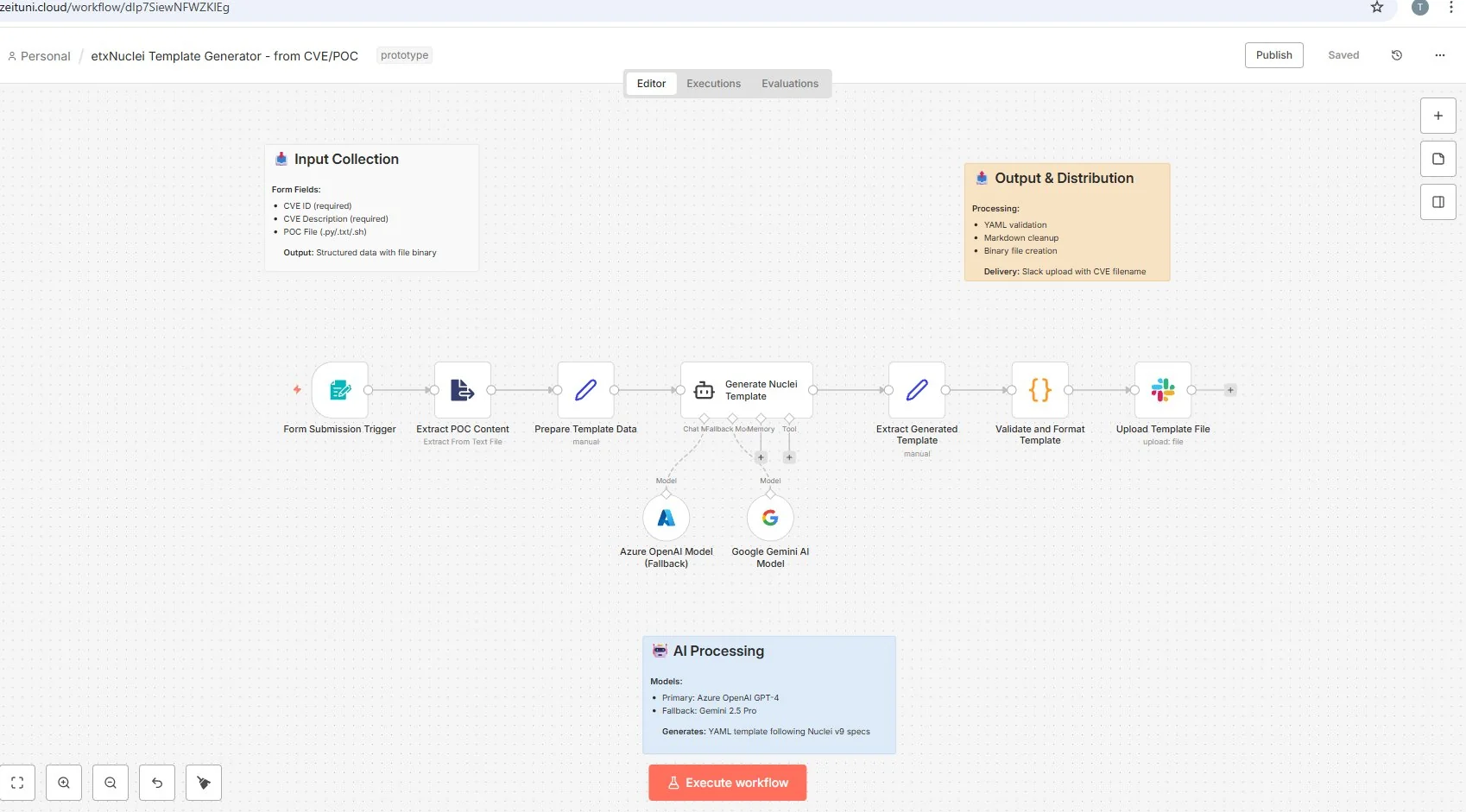
Automated Bug Bounty Suite
Built a fully automated bug bounty reconnaissance pipeline using n8n workflows, integrating AI Agent with Google Gemini for intelligent analysis, webhook triggers, memory nodes, and structured output formatting.
View on GitHub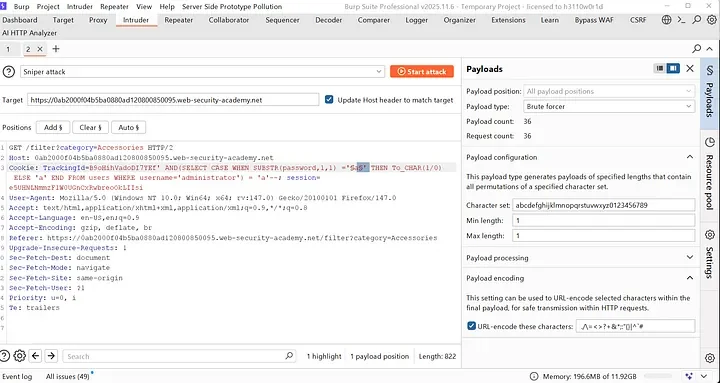
Blind SQL Injection — Conditional Errors
Hands-on lab writeup covering blind SQL injection via conditional error responses. Documented exploitation technique, payload crafting, and database enumeration without visible output — published on Medium.
Read on Medium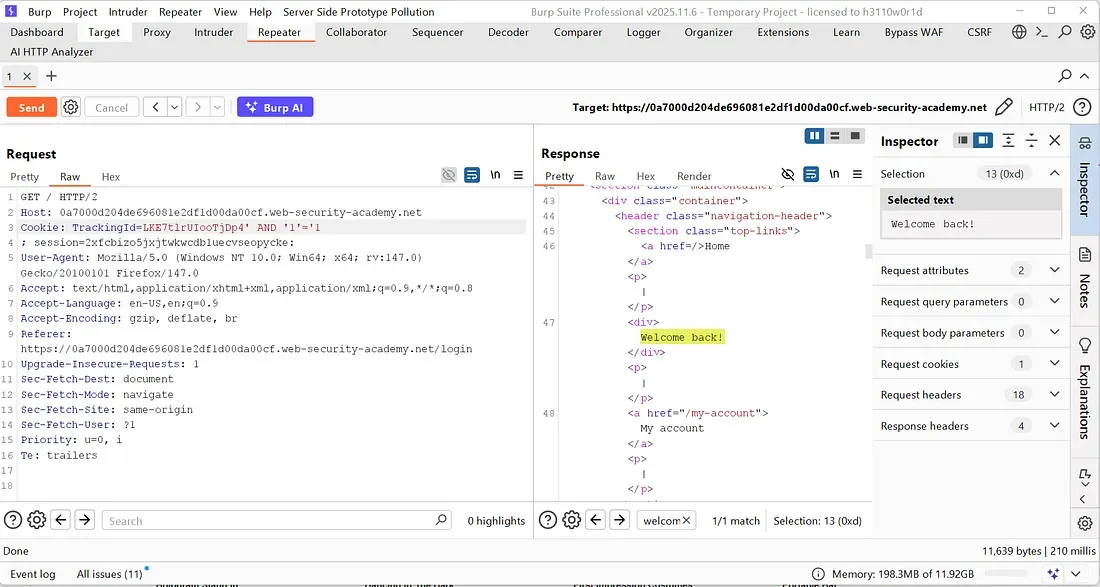
Blind SQL Injection — Conditional Responses
Deep-dive analysis into boolean-based blind SQL injection using conditional response differences. Covers detection methodology, automated extraction, and mitigation — published on Medium.
Read on Medium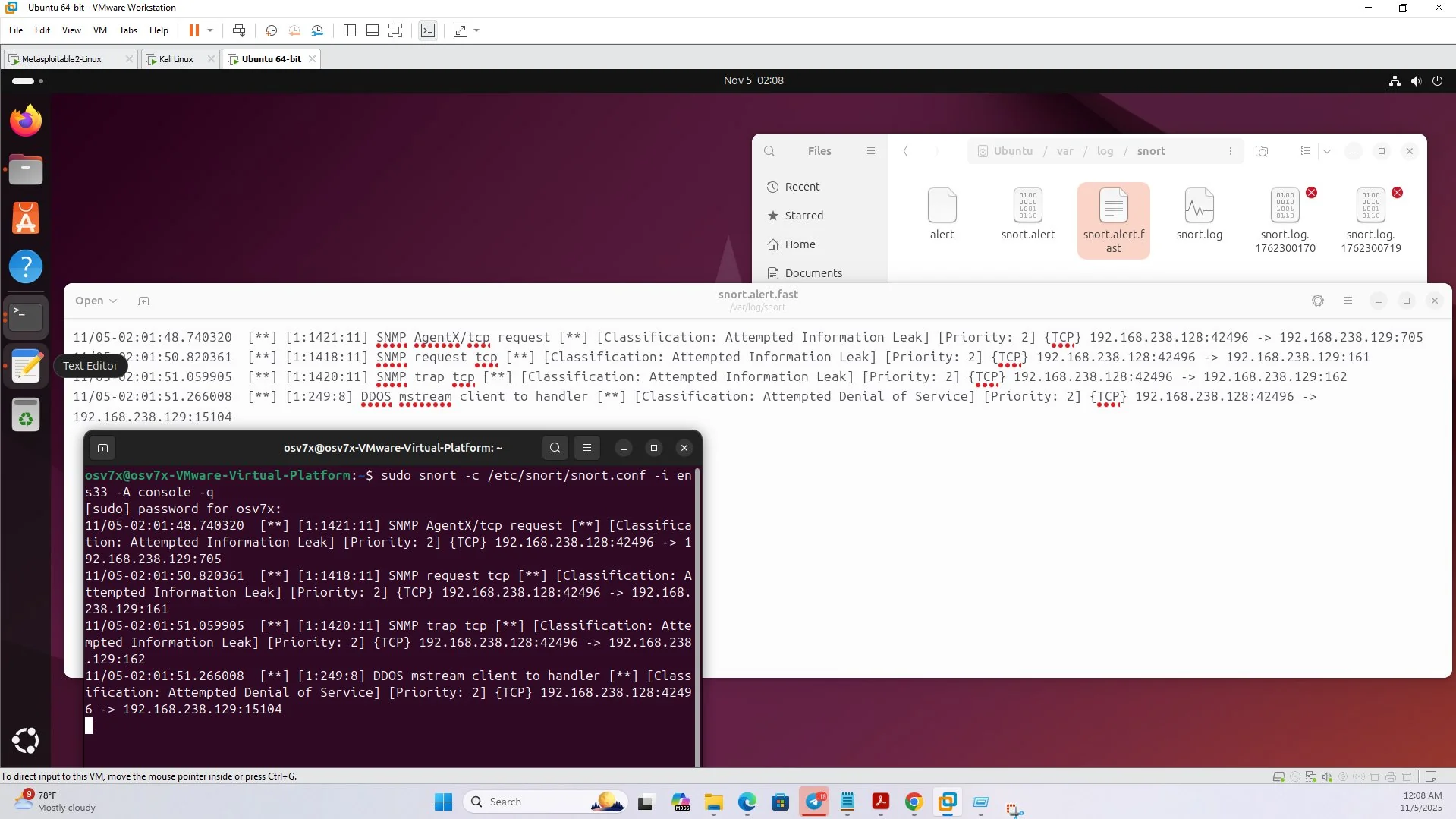
Snort IDS — Intrusion Detection Lab
Deployed Snort IDS in a VMware lab environment to detect real attack scenarios: SNMP enumeration, DDoS via hping3, and Telnet brute-force attempts. Wrote custom detection rules and analyzed alert logs from live attack simulations using Kali Linux against Metasploitable2.
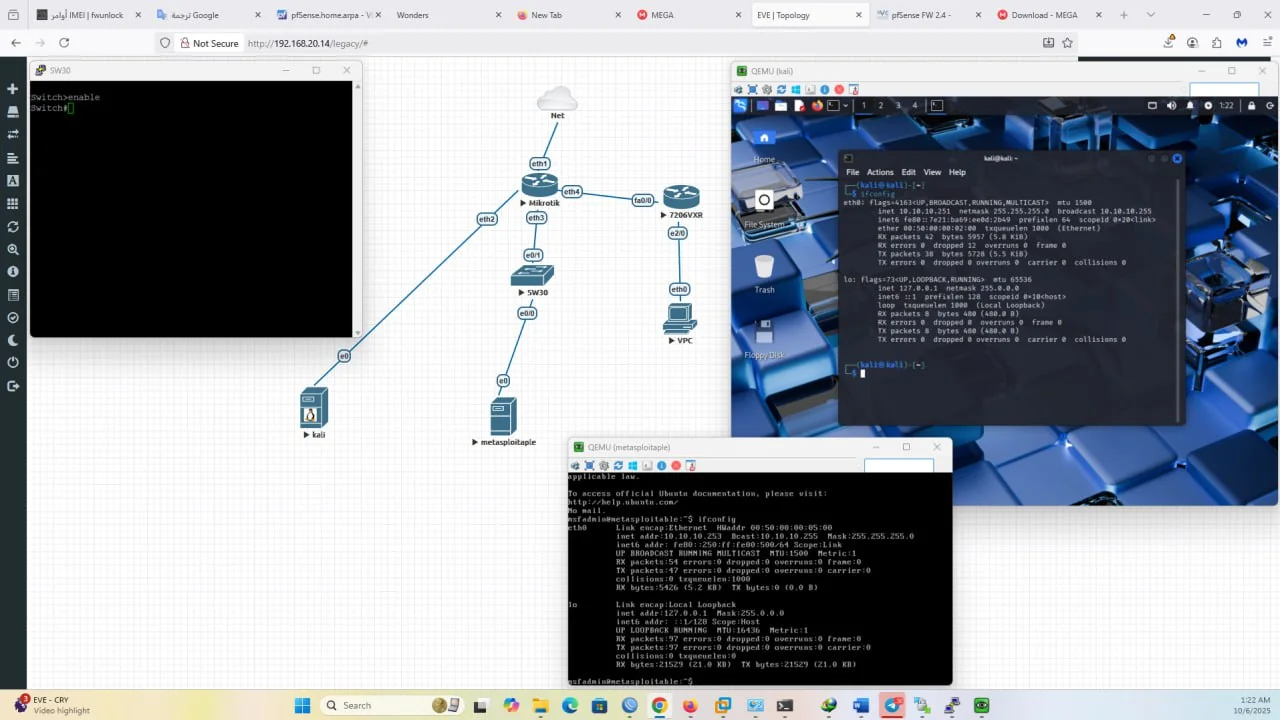
EVE-NG Network Simulation Lab
Built a full network simulation environment on a personal ESXi server running EVE-NG. Lab includes Mikrotik routers, Kali Linux, Metasploitable2, and VPC nodes for practicing network attacks, routing configurations, and penetration testing in a fully isolated environment.
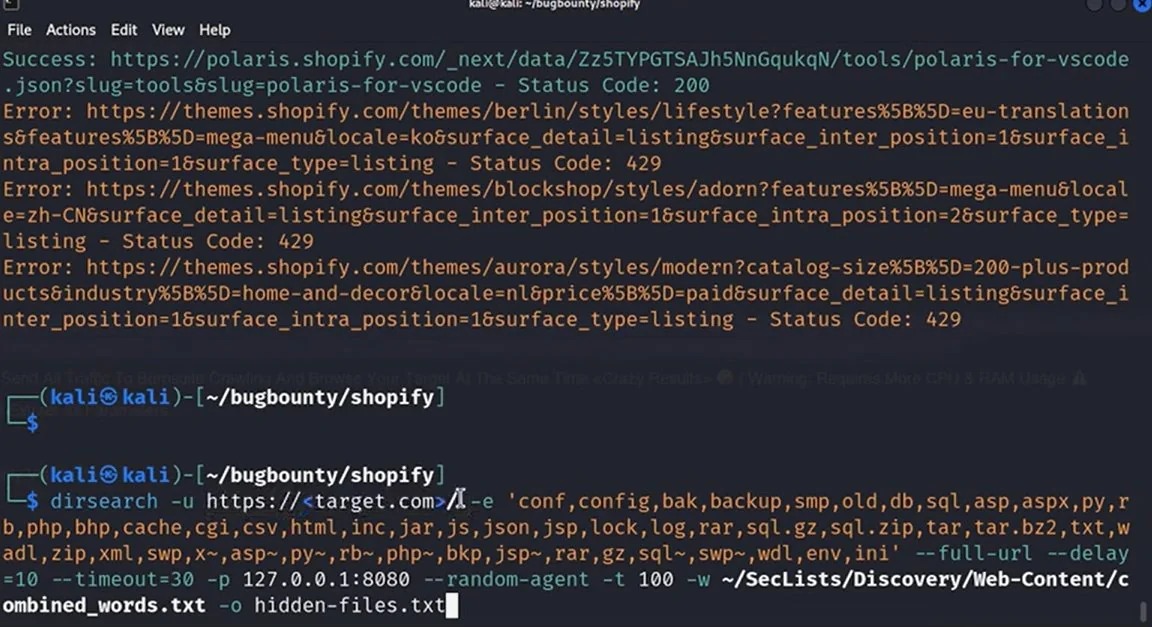
Web Recon & Directory Enumeration
Performed active web reconnaissance on bug bounty targets using dirsearch with custom wordlists, proxy routing through Burp Suite, and randomized user-agents to bypass rate limiting. Discovered hidden endpoints and backup files across multiple targets.
Get In Touch
Open to security engagements, network consulting, bug bounty collaborations, and freelance development — let's talk.
Whether you need a penetration test, network infrastructure review, security consultation, or a modern web application built with security in mind — I'm available. Reach out through any channel below and I'll respond as soon as possible.